Instalacija Davaoca Identiteta (Shibboleth IdP 5.1.2) - Debian/Ubuntu
Priprema pred instalaciju¶
Hardverski zahtevi¶
Hardverski zahtevi:
- CPU: 2 Core (64 bit)
- RAM: 4 GB
- HDD: 20 GB
- OS: Debian 12 / Ubuntu 22.04
Softver koji će biti instaliran¶
Softver koji će biti instaliran:
- ca-certificates
- Shibboleth Identity Provider (<= 5.0.0)
- OpenSSL (<= 3.0.2)
- Jetty 11+ Servlet Container (implementing Servlet API 5.0 or above)
- Amazon Corretto JDK 17
- Apache Web Server (>= 2.4)
Podesiti IP TABLES¶
Najpre je potrebno instalirati iptables softverski paket i izvršiti početna podešavanja ukoliko već niste.
Otvoriti portove 80 (HTTP) i 443 (HTTPS)
To se može uraditi na sledeći način:
Otvoriti port 80 i 443 dodavanjem sledećih linija u fajl:
-A INPUT -s xxx.xxx.xxx.xxx/255.255.255.xxx -p tcp -m tcp --dport 80 -j ACCEPT
-A INPUT -s xxx.xxx.xxx.xxx/255.255.255.xxx -p tcp -m tcp --dport 443 -j ACCEPT
Napomena: Navedene linije je potrebno uneti bavezno iznad linije: -A INPUT -j REJECT --reject-with icmp-host-prohibited
Sačuvati izmene:
Podesiti hosta¶
U okviru čitavog uputstva smatraće se da je domen VM idp.institucija.ac.rs, tako da na svim mestima umesto ovog naziva domena potrebno je da unesete naziv po vašem izboru.
Veoma je važno da FQDN (Full Qualified Domain Name) i pun hostname (# hostname -f) ove VM, npr. idp.institucija.ac.rs, koji se podešava u okviru ove sekcije bude isti kao i domen koji je adekvatno podešen na DNS serveru, a taj domen će se takođe kasnije koristiti za kreiranje sertifikata.
Podešavanje host podataka
Dat je primer postavljanja idp.institucija.ac.rs kao FQDN podatka, koji je potrebno zameniti FQDN podatkom Vašeg Davaoca Identiteta, kao i postavljanja HOSTNAME podatka: idp, koji je potrebno zameniti hostname podatkom Vašeg Davaoca Identiteta.
Na kraju fajla se unosi linija u formi: IP ADRESA FQDN HOSTNAME Npr:
Postaviti hostname
Koristi se komanda sledeće forme: hostnamectl set-hostname HOSTNAME
Konfiguracija okruženja¶
Postaviti varijablu JAVA_HOME:
Instalacija neophodnih softverskih paketa¶
Instalirati Apache web server¶
Instalirati Amazon Corretto JDK¶
Preuzeti javni ključ B04F24E3.pub u /tmp direktorijum kako bi se verifikovao potpisan fajl sa AMAZON-a (https://docs.aws.amazon.com/corretto/latest/corretto-17-ug/downloads-list.html#signature)
Konvertovanje javnog ključa u "amazon-corretto.gpg":
gpg --no-default-keyring --keyring /tmp/temp-keyring.gpg --export --output /etc/apt/keyrings/amazon-corretto.gpg
Kreiranje APT source liste neophodne za Amazon Corretto:
echo "deb [arch=amd64 signed-by=/etc/apt/keyrings/amazon-corretto-jdk.asc] https://apt.corretto.aws stable main" >> /etc/apt/sources.list.d/amazon-corretto.list
Instalirati Amazon Corretto:
Provera verzije instaliranog Java paketa:
Instalirati Jetty Servlet Container¶
Preuzeti Jetty 11:
Kreirati jetty-src folder kao simbolički link. Ovo će biti korisno za ažuriranje Jetty softvera u budućnosti:
Kreirati jetty korisnika:
Podesiti Jetty konfiguraciju koja će da pregazi inicijalnu i koja će da podnese ažuriranje:Kreirati /opt/jetty/tmp direktorijum tako da se koristi od strane Jetty softvera:
Kreirati Jetty Log direktorijume:
Preuzeti fajl jetty:
Omogućiti da jetty servis može da se učitava iz komandne linije (loadable):
Odaberite editor sa kojim ste najbolje upoznatiPotrebno je da se u fajlu /etc/systemd/system/jetty.service zameni PIDFile=/opt/web/mybase/jetty.pid sa PIDFile=/opt/jetty/jetty.pid putanjom.
Instalirati Servlet Jakarta API 5.0.0:
Instalirati i konfigurisati LogBack:
wget "https://docs.amres.ac.rs/download/shibboleth/5.1.2/jetty-requestlog.xml" -O /opt/jetty/etc/jetty-requestlog.xml
wget "https://docs.amres.ac.rs/download/shibboleth/5.1.2/jetty-logging.properties" -O /opt/jetty/resources/jetty-logging.properties
Proveriti da li su podešavanja u redu:
Izveštaj izvršene komande:
Jetty NOT running
Izveštaj izvršene komande:
Jetty running pid=XXXX
Ukoliko se prikaže greška "Job for jetty.service failed because the control process exited with error code. See "systemctl status jetty.service" and "journalctl -xe" for details.", pokušajte sledeće:
Instalacija Davaoca Identiteta ( Shibboleth IdP 5.1.2 )¶
Preuzeti i otpakovati Shibboleth Identity Provider v5.1.2 repozitorijum na lokaciju /usr/local/src:
wget https://shibboleth.net/downloads/identity-provider/5.1.2/shibboleth-identity-provider-5.1.2.tar.gz
Pokrenuti skriptu za instalaciju:
U procesu instalacije biće ispisana sledeća obaveštenja i biće postavljena pitanja.
Kada se prikažu određene linije koje su markirane bojom u nastavku potrebno je uneti odgovarajuće podatke:
- Installation Directory: [/opt/shibboleth-idp] ? Klik ENTER
- SAML EntityID: [https://idp.institucija.ac.rs/idp/shibboleth] ? Klik ENTER
- Attribute Scope: [institucija.ac.rs] ? Klik ENTER
Objašnjenje :
- Attribute Scope: Scope treba da bude validan domen institucije
Napomena:
Od ovog momenta, promenljiva idp.home odnosi se na direktorijum: /opt/shibboleth-idp
Installation Directory: [/opt/shibboleth-idp] ?
INFO - New Install. Version: 5.1.2
INFO - Creating idp-signing, CN = idp.institucija.ac.rsidp.institucija.ac.rs URI = https://idp.institucija.ac.rs/idp/shibboleth, keySize=3072
INFO - Creating idp-encryption, CN = idp.institucija.ac.rs URI = https://idp.institucija.ac.rs/idp/shibboleth, keySize=3072
INFO - Creating backchannel keystore, CN = idp.institucija.ac.rs URI = https://idp.institucija.ac.rs/idp/shibboleth, keySize=3072
INFO - Creating Sealer KeyStore
INFO - No existing versioning property, initializing...
SAML EntityID: [https://idp.institucija.amres.ac.rs/idp/shibboleth] ?
Attribute Scope: [institucija.amres.ac.rs] ?
INFO - Initializing OpenSAML using the Java Services API
INFO - Algorithm failed runtime support check, will not be usable: http://www.w3.org/2001/04/xmlenc#ripemd160
INFO - Algorithm failed runtime support check, will not be usable: http://www.w3.org/2001/04/xmldsig-more#hmac-ripemd160
INFO - Algorithm failed runtime support check, will not be usable: http://www.w3.org/2001/04/xmldsig-more#rsa-ripemd160
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/ldap.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/c14n/subject-c14n.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/services.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/authn/authn.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/saml-nameid.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/conf/admin/admin.properties
INFO - Creating Metadata to /opt/shibboleth-idp/metadata/idp-metadata.xml
INFO - Rebuilding /opt/shibboleth-idp/war/idp.war, Version 5.1.2
INFO - Initial populate from /opt/shibboleth-idp/dist/webapp to /opt/shibboleth-idp/webpapp.tmp
INFO - Overlay from /opt/shibboleth-idp/edit-webapp to /opt/shibboleth-idp/webpapp.tmp
INFO - Creating war file /opt/shibboleth-idp/war/idp.war
Onemogućiti Jetty Directory indeksiranje¶
Kreirati direktorijum koji nedostaje:
Izvršite rebild IdP war fajla:
Konfiguracija Apache Web servera¶
Kreirati DocumentRoot:
Komercijalni SSL sertifikat¶
Kreiranje komercijalnog SSL sertifikata i ključa:
Komercijalni sertifikat i ključ treba da budu vrste GÉANT OV SSL kog kreirate po uputstvu:
- HTTPS Server Certificate (Public Key) - (idp.institucija.ac.rs.crt) u /etc/ssl/certs
- HTTPS Server Key (Private Key) - (idp.institucija.ac.rs.key) u /etc/ssl/private
Jedna od mogućnosti kako se to može uraditi:
Preuzme se fajl SCSreq.cnf na lokaciju /etc/ssl/private/SCSreq.cnf
Generisati privatni ključ (.key) i zahtev (.csr):
openssl req -new -sha256 -config /etc/ssl/private/SCSreq.cnf -utf8 -keyout /etc/ssl/private/$(hostname -f).key -out /etc/ssl/private/$(hostname -f).csr
Primer postupka kreiranja privatnog ključa i zahteva (koristitli biste drugačiji naziv sertifikata i uneli biste odgovarajuće podatke):
openssl req -new -sha256 -config /etc/ssl/private/SCSreq.cnf -utf8 -keyout /etc/ssl/private/$(hostname -f).key -out /etc/ssl/private/$(hostname -f).csr
Generating a 2048 bit RSA private key
....................+++
....................+++
writing new private key to '/etc/ssl/private/idp.institucija.ac.rs.key'
-----
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Oznaka zemlje (2 znaka) [RS]: Klik Enter
Pun naziv drzave []: Klik Enter
Lokacija (mesto) []: Belgrade
Postanski broj []: 11000
Ulica i broj []: Bulevar kralja Aleksandra 90
Zvanični naziv institucije []: Academic network of the Republic of Serbia – AMRES
FQDN adresa servera []: idp.institucija.ac.rs
Zatim generisani zahtev iskorititi za kreiranje sertifikata (javnog ključa) koji treba da bude tipa GÉANT OV SSL
Preuzimanje CA Cert (GEANT_OV_RSA_CA_4.crt) sertifikata:
wget https://docs.amres.ac.rs/download/shibboleth/GEANT_OV_RSA_CA_4.crt -O /etc/ssl/certs/GEANT_OV_RSA_CA_4.crt
Dati odgovarajuće privilegije SSL sertifikatu i ključu:
Omogućiti Apache2 modul:
Zatim treba restartovati Apache proces:
Konfiguracija Jetty Context Descriptor za Davaoca Identiteta¶
Konfigurisati IdP Context Descriptor. Kreirati direktorijum /opt/jetty/webapps:
Preuzeti fajl idp.xml:
Postaviti da vlasnik glavnih direktorijuma Davaoca Identiteta bude jetty:
Restartovati Jetty servis:
Konfiguracija - Apache2 (front-end Jetty)¶
Kreirati VirtualHost file:
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/000-idp.institucija.ac.rs.conf -O /etc/apache2/sites-available/$(hostname -f).conf
Fajl /etc/apache2/sites-available/$(hostname -f).conf je potrebno izmeniti. Uneti nazive sertifikata i ključa i podatke o serveru.
Fajl /etc/apache2/sites-available/000-$(hostname -f).conf sa svim potrebnim izmenama:
Dodati Apache2 kreirane virtualne hostove:
Ukoliko se prikaže greška proverite:
- Da li ste kreirali privatni ključ i sertifikat i uneli ga na pravilnu lokaciju?
- Da li ste preuzeli GEANT_OV_RSA_CA_4.crt sertifikat?
- Da li ste uneli sve potrebne izmene u okviru fajla /etc/apache2/sites-available/$(hostname -f).conf?
- Da li ste omogućili Apache2 modul prema uputstvu?
- Da li ste instalirali sav potreban softver prema uputstvu (ca-certificates openssl apache2)?
Proveriti IdP metapodatke, koji su dostupni na linku u formi: https://DOMEN_VM/idp/shibboleth
Konfiguracija skladišta Davaoca Identiteta¶
Koriščen je princip: HTML lokalno skladište, GCM enkripcija, bez baze podataka i nije potrebno ništa dodatno konfigurisati.
Proveriti status Davaoca Identiteta:
### Operating Environment Information
operating_system: Linux
operating_system_version: 6.1.0-21-amd64
operating_system_architecture: amd64
jdk_version: 17.0.11
available_cores: 2
used_memory: 143 MB
maximum_memory: 1778 MB
### Identity Provider Information
idp_version: 5.1.2
start_time: 2024-06-06T15:11:00.855Z
current_time: 2024-06-06T15:11:02.370367340Z
uptime: PT1.515S
enabled modules:
idp.Core (Core IdP Functions (Required))
idp.CommandLine (Command Line Scripts)
idp.EditWebApp (Overlay Tree for WAR Build)
idp.authn.Password (Password Authentication)
idp.admin.Hello (Hello World)
installed plugins:
service: shibboleth.LoggingService
last successful reload attempt: 2024-06-06T15:01:56.729374635Z
last reload attempt: 2024-06-06T15:01:56.729374635Z
service: shibboleth.AttributeFilterService
last successful reload attempt: 2024-06-06T15:02:00.429587328Z
last reload attempt: 2024-06-06T15:02:00.429587328Z
service: shibboleth.AttributeResolverService
last successful reload attempt: 2024-06-06T15:02:00.539291194Z
last reload attempt: 2024-06-06T15:02:00.539291194Z
No Data Connector has ever failed
service: shibboleth.AttributeRegistryService
last successful reload attempt: 2024-06-06T15:01:59.727803890Z
last reload attempt: 2024-06-06T15:01:59.727803890Z
service: shibboleth.NameIdentifierGenerationService
last successful reload attempt: 2024-06-06T15:02:00.648774869Z
last reload attempt: 2024-06-06T15:02:00.648774869Z
service: shibboleth.RelyingPartyResolverService
last successful reload attempt: 2024-06-06T15:02:00.709470138Z
last reload attempt: 2024-06-06T15:02:00.709470138Z
service: shibboleth.MetadataResolverService
last successful reload attempt: 2024-06-06T15:02:00.133460957Z
last reload attempt: 2024-06-06T15:02:00.133460957Z
No Metadata Resolver has ever attempted a reload
service: shibboleth.ReloadableAccessControlService
last successful reload attempt: 2024-06-06T15:02:01.408871260Z
last reload attempt: 2024-06-06T15:02:01.408871260Z
service: shibboleth.ReloadableCASServiceRegistry
last successful reload attempt: 2024-06-06T15:02:01.452175673Z
last reload attempt: 2024-06-06T15:02:01.452175673Z
service: shibboleth.ManagedBeanService
last successful reload attempt: 2024-06-06T15:02:01.471856987Z
last reload attempt: 2024-06-06T15:02:01.471856987Z
Integracija sa OpenLDAP bazom podataka¶
Instalirati ldap-utils paket:
Kreirati sistemski nalog (nalog za monitoring) u OpenLDAP bazi
O tome možete da pročitate u ovom delu uputstva Instalacije i konfiguracije OpenLDAP baze podataka (Debian/Ubuntu) ili ovde (CentOS).
Nakon što kreirate sistemski nalog potrebno je da mu se daju privilegije čitanja (monitoringa) korisničkih naloga u bazi, što se postiže sastavljanjem liste za kontrolu pristupa o čemu možete da pročitate više u ovom delu (Debian/Ubuntu) ili pročitati deo (CentOS) .
Napomena: Ukoliko vam je potrebna konsultacija oko specifičnije liste za kontrolu pristupa kontaktirajte nas na imejl adresu helpdesk@amres.ac.rs.
OpenLDAP sertifikat
Ukoliko se OpenLDAP baza ne nalazi na VM na kojoj se instalira i konfiguriše Shibboleth IdP potrebno je preneti sertifikat baze na ovu VM jer će biti neophodan za ostvarivanje sigurne konekcije sa bazom podataka. Sertifikat se može preneti na lokaciju /etc/ldap/ ili /etc/ldap/certs ili neku vama pogodnu lokaciju. Podatak o lokaciji ovog sertifikata treba da se unese kasnije u fajl /opt/shibboleth-idp/conf/ldap.properties.
Koristi se metoda OpenLDAP + STARTTLS.
Fajl secrets.properties¶
Izmena fajla secrets.properties :
Potrebno je editovati liniju:
- Umesto dela myServicePassword unosi lozinka sistemskog naloga koji će povezati IdP sa LDAP bazom podataka i na taj način omogučiti autentifikaciju korisnika iz baze:
Fajl ldap.properties¶
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/ldap.properties -O /opt/shibboleth-idp/conf/ldap.properties
U fajl ldap.properties se navode pojedinosti vezane za LDAP bazu sa kojom se IdP povezuje:
idp.authn.LDAP.ldapURL = ldap://<DOMEN VM NA KOJOJ_JE LDAP BAZA> npr. ldap://ldap.institucija.ac.rs
idp.authn.LDAP.trustCertificates = <PUTANJA_DO_LDAP_SERTIFIKATA> npr. /etc/ldap/ldap.institucija.ac.rs.crt
idp.authn.LDAP.baseDN = <DEO LDAP BAZE GDE SU KORISNIČKI NALOZI KOJI SE AUTENTIFIKUJU> npr. ou=people,dc=institucija,dc=ac,dc=rs
idp.authn.LDAP.subtreeSearch = false
idp.authn.LDAP.bindDN = <DN SISTEMSKOG NALOGA> npr. cn=idpuser,ou=system,dc=institucija,dc=ac,dc=rs
idp.attribute.resolver.LDAP.exportAttributes = <ATRIBUTI KOJI SE UZIMAJU IZ LDAP BAZE> npr. cn givenName sn mail rsEduPersonAffiliation displayName eduPersonEntitlement rsEduPersonLocalNumber Napomena:
- U primeru iznad vrednost parametra idp.authn.LDAP.baseDN je navedena organizaciona jedinica u kojoj se nalaze svi korisnički nalozi koji se autentifikuju. Ukoliko je Vaša baza podataka kreirana tako da su nalozi organizovani u više grana i organizacionih jedinica, vrednost parametra idp.authn.LDAP.baseDN treba da bude koren LDAP stabla, a vrednost parametra idp.authn.LDAP.subtreeSearch treba da bude true
- eduPersonEntitlement je specijalna vrsta atributa koji se koristi za autorizaciju. Može se koristiti da bi se utvrdilo da li korisnik ima pravo da koristi određeni servis.
- rsEduPersonAffiliation atribut definiše način na koji je osoba povezana sa institucijom (moguće vrednosti su: student, učenik, nastavni kadar, zaposleni, spoljni saradnik, korisnik usluge, gost).
- rsEduPersonLocalNumber atribut predstavlja lokalni identifikator osobe, npr. za studenta broj studenta ili za zaposlenog broj zaposlenog.
Primer popunjenog fajla ldap.properties:
Provera konektivnosti sa LDAP bazom
ldapsearch -x -H ldap://<FQDN ili IP adresa> -D '<DN_SISTEMSKOG_NALOGA>' -w '<IDPUSER_PASSWORD>' -b 'ou=people,dc=example,dc=org' '(uid=<KORISNIČKO_IME>)'
<FQDN ili IP adresa> zameniti podatkom o domenu (FQDN) ili IP adresi virtuelne mašine na kojoj je LDAP baza
<DN_SISTEMSKOG_NALOGA> zameniti podatkom o kreiranom sistemskom nalogu npr. cn=idpuser,ou=system,dc=institucija,dc=ac,dc=rs
<IDPUSER_PASSWORD> zameniti lozinkom sistemskog naloga
ou=people,dc=example,dc=org zameniti podatkom o delu LDAP baze gde su korisnički nalozi koji se autentifikuju npr. ou=people,dc=institucija,dc=ac,dc=rs
<KORISNIČKO_IME> zameniti podatkom o korisničkom imenu test naloga za kog se proverava uspešnost autentifikacije Primer komande:
Ukoliko ste preneli OpenLDAP sertifikat sa druge mašine, neophodne je da mu se dodele određene privilegije
chown jetty:root /opt/shibboleth-idp/credentials/ldap-server.crt ; chmod 600 /opt/shibboleth-idp/credentials/ldap-server.crt
Restartovati Jetty proces:
Proveriti status Davaoca Identiteta. Napomena: Ukoliko je izveštaj isti kao prethodni put sa konfiguracijom je sve u redu:
Podesiti da Davaoc Identiteta kreira persistent NameID¶
Shibboleth Documentation: https://shibboleth.atlassian.net/wiki/spaces/IDP5/pages/3199507892/PersistentNameIDGenerationConfiguration
persistent NameID je jedinstveni trajni identifikator korisnika, koji Davalac Identiteta prosleđuje Davaocu Servisa.
Strategija A "Computed mode" (preporučena):¶
mv /opt/shibboleth-idp/conf/saml-nameid.properties /opt/shibboleth-idp/conf/saml-nameid.properties_default
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/saml-nameid.properties -O /opt/shibboleth-idp/conf/saml-nameid.properties
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/saml-nameid.xml -O /opt/shibboleth-idp/conf/saml-nameid.xml
Rezultat komande je potrebno sačuvati/kopirati, jer se primenjuje u sledećem koraku
Rezultat komande je niz karaktera formata:
4Z4VL1gOzw*******************************
- Otkomentarisati liniju:
- Deo changethistosomethingrandom izmeniti dobijenim nizom karaktera dobijenim kao rezultat prethodno primenjene komande (openssl rand -base64 36).
Restartovati Jetty proces:
Proveriti status Davaoca Identiteta:
Strategija B "Stored mode" (korišćenje baze podataka za skladištenje persistent NameID)¶
Instalirati potrebne pakete:
apt install default-mysql-server libmariadb-java libcommons-dbcp2-java libcommons-pool2-java --no-install-recommends
Instalirati JDBCStorageService plugin:
Izveštaj pokrenute komande:
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/admin/admin.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/ldap.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/authn/authn.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/c14n/subject-c14n.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/saml-nameid.properties
INFO - Including auto-located properties in /opt/shibboleth-idp/bin/../conf/services.properties
INFO - Downloading from HTTPResource [http://shibboleth.net/downloads/identity-provider/plugins/jdbc/2.0.0/java-plugin-jdbc-storage-2.0.0.tar.gz]
INFO - Downloading from HTTPResource [http://shibboleth.net/downloads/identity-provider/plugins/jdbc/2.0.0/java-plugin-jdbc-storage-2.0.0.tar.gz.asc]
INFO - Plugin net.shibboleth.plugin.storage.jdbc: Trust store folder does not exist, creating
INFO - Plugin net.shibboleth.plugin.storage.jdbc: Trust store does not exist, creating
INFO - TrustStore does not contain signature 0x7D27E610B8A3DC52
Accept this key:
Signature: 0x7D27E610B8A3DC52
FingerPrint: B5B5DD332142AD657E8D87AC7D27E610B8A3DC52
Username: Philip David Smart <philip.smart@jisc.ac.uk>
[yN] y
INFO - Installing Plugin 'net.shibboleth.plugin.storage.jdbc' version 2.0.0
INFO - Rebuilding /opt/shibboleth-idp/war/idp.war, Version 5.1.2
INFO - Initial populate from /opt/shibboleth-idp/dist/webapp to /opt/shibboleth-idp/webpapp.tmp
INFO - Overlay from /opt/shibboleth-idp/dist/plugin-webapp to /opt/shibboleth-idp/webpapp.tmp
INFO - Overlay from /opt/shibboleth-idp/edit-webapp to /opt/shibboleth-idp/webpapp.tmp
INFO - Creating war file /opt/shibboleth-idp/war/idp.war
Pokrenuti bazu:
Pokrenuti proces uspostavljanja bezbedonosne politike MariaDB baze podataka (ukoliko već nije uspostavljena):
Pokretanjem ove komande ulazi se u interaktivni mod, u okviru koga je potrebno odgovotiri na sledeća pitanja:
Kreirati shibpid tabelu u shibboleth bazi podataka:
Potrebno je editovati ###SHIBPID-USERNAME-CHANGEME### i ###SHIB-DB-USER-PASSWORD-CHANGEME### delove konfiguracije u fajlu /root/shib-pid-db.sql, čime ćete kreirati korisnika koji će biti korišćen kasnije.
Importovati bazu:
Restartovati MariaDB servis:Pokrenuti build skripte za dodavanje neophodnih biblioteka:
Omogućiti konekciju sa bazom izmenom sledećeg fajla:
Dodati deo konfiguracije pre poslednjeg taga:U delu ###SHIB-USERNAME-CHANGEME### i ###SHIB-DB-USER-PASSWORD-CHANGEME### unesite kredencijale prethodno kreiranog korisnika.
<bean id="shibpid.JDBCStorageService.DataSource"
class="org.apache.commons.dbcp2.BasicDataSource" destroy-method="close" lazy-init="true"
p:driverClassName="org.mariadb.jdbc.Driver"
p:url="jdbc:mysql://localhost:3306/shibpid?autoReconnect=true"
p:username="###_SHIBPID-USERNAME-CHANGEME_###"
p:password="###_SHIBPID-DB-USER-PASSWORD-CHANGEME_###"
p:maxTotal="10"
p:maxIdle="5"
p:maxWaitMillis="15000"
p:testOnBorrow="true"
p:validationQuery="select 1"
p:validationQueryTimeout="5" />
Omogućite kreiranje persistent-id vrednosti preuzimanjem konfiguracionog fajla:
mv /opt/shibboleth-idp/conf/saml-nameid.properties /opt/shibboleth-idp/conf/saml-nameid.properties_default
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/saml-nameid_stored.properties -O /opt/shibboleth-idp/conf/saml-nameid.properties
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/saml-nameid.xml -O /opt/shibboleth-idp/conf/saml-nameid.xml
Rezultat komande je potrebno sačuvati/kopirati, jer se primenjuje u sledećem koraku
Rezultat komande je niz karaktera formata:
4Z4VL1gOzw*******************************
- Otkomentarisati liniju:
- Deo changethistosomethingrandom izmeniti dobijenim nizom karaktera dobijenim kao rezultat prethodno primenjene komande (openssl rand -base64 36).
mv /opt/shibboleth-idp/conf/c14n/subject-c14n.xml /opt/shibboleth-idp/conf/c14n/subject-c14n.xml_default
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/subject-c14n.xml -O /opt/shibboleth-idp/conf/c14n/subject-c14n.xml
mv /opt/shibboleth-idp/conf/c14n/subject-c14n.properties /opt/shibboleth-idp/conf/c14n/subject-c14n.properties_default
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/subject-c14n.properties -O /opt/shibboleth-idp/conf/c14n/subject-c14n.properties
Restartovati Jetty proces:
Proveriti status Davaoca Identiteta:
Podešavanje attribute-resolver.xml fajla¶
Preuzeti fajl attribute-resolver.xml:
mv /opt/shibboleth-idp/conf/attribute-resolver.xml /opt/shibboleth-idp/conf/attribute-resolver_default.xml
U slučaju da ste odabrali Strategiju A "Computed mode" (preporučena) za persistent NameID, preuzimate sledeći fajl:
U slučaju da ste odabrali Strategiju B "Stored mode" za persistent NameID, preuzimate sledeći fajl:
U fajlu treba izmeniti sledeće:
Neophodno je izmeniti #sHO# podatak:
#sHO# predstavlja SCHAC code institucije koja je registrovana u Erazmus+ projektu. Spisak institucija možete pronaći na linku https://wiki.geant.org/display/SM/ECHE+Whitelist (pretražite RS country code). Više o tome na https://docs.amres.ac.rs/uputstva/shibboleth/esi/#o-esi-atributu .
Umesto dela Naziv Vaše institucije uneti naziv Vaše institucije.
Dodatno objašnjenje sadržaja fajla attribute-resolver.xml
U okviru fajla dodata je definicija za Pairwise identifikator koji ima istu ulogu kao eduPersonTargetedID atribut i kreira se od iste persistentId vrednosti. Bitno je napomenuti da će uskoro eduPersonTargetedID atribut prestati da se koristi.
Ukoliko želite da učestvujete u Erazmus+ projektu i imate HEI ulogu, potrebno je da dodate konfiguraciju za ESI atribut.
Promeniti vlasnika fajla:
Instalirati plugin koji omogućava definiciju ScriptedAttribute:
Izveštaj pokrenute komande:
Restartovati Jetty proces:
Proveriti status Davaoca Identiteta:
Podesiti da Shibboleth Identity Provider oslobađa eduPersonTargetedID¶
Trajni identifikator korisnika koji razmenjuju Davalac Servisa i Davalac Identiteta (Shibboleth IdP). Nikada se ne dodeljuje ponovo i ne sadrži nikakve podatke o korisniku. Davalac Identiteta smešta persistentId vrednost u eduPersonTargetedID atribut kada komunicira sa određenim Davaocem Servisa ukoliko on to zahteva.
Dodatno objašnjenje:
U okviru fajla attribute-resolver.xml dodata je definicija za Pairwise identifikator koji ima istu ulogu kao eduPersonTargetedID atribut i kreira se od iste persistentId vrednosti. Bitno je napomenuti da će uskoro eduPersonTargetedID atribut prestati da se koristi.
Ovaj deo je već podešen u okviru fajla attribute-resolver.xml koji ste preuzeli i izmenili u prethodnim koracima.
Dodatno, potrebno je preuzeti fajl eduPersonTargetedID.properties.
wget https://docs.amres.ac.rs/download/shibboleth/eduPersonTargetedID.properties -O /opt/shibboleth-idp/conf/attributes/custom/eduPersonTargetedID.properties ; chown jetty:root /opt/shibboleth-idp/conf/attributes/custom/eduPersonTargetedID.properties
Restartovati Jetty proces:
Proveriti status Davaoca Identiteta:
Uneti dodatne šeme za definisanje atributa¶
rm /opt/shibboleth-idp/conf/attributes/eduPerson.xml ; wget https://docs.amres.ac.rs/download/shibboleth/eduPerson.xml -O /opt/shibboleth-idp/conf/attributes/eduPerson.xml
rm /opt/shibboleth-idp/conf/attributes/inetOrgPerson.xml ; wget https://docs.amres.ac.rs/download/shibboleth/inetOrgPerson.xml -O /opt/shibboleth-idp/conf/attributes/inetOrgPerson.xml
rm /opt/shibboleth-idp/conf/attributes/samlSubject.xml ; wget https://docs.amres.ac.rs/download/shibboleth/samlSubject.xml -O /opt/shibboleth-idp/conf/attributes/samlSubject.xml
Preuzeti rsEdu.xml i schac.xml šemu na lokaciju /opt/shibboleth-idp/conf/attributes/
wget https://docs.amres.ac.rs/download/shibboleth/rsEdu.xml -O /opt/shibboleth-idp/conf/attributes/rsEdu.xml ; chown jetty:root /opt/shibboleth-idp/conf/attributes/rsEdu.xml
wget https://docs.amres.ac.rs/download/shibboleth/schac.xml -O /opt/shibboleth-idp/conf/attributes/schac.xml ; chown jetty:root /opt/shibboleth-idp/conf/attributes/schac.xml
Preuzeti fajl default-rules.xml :
mv /opt/shibboleth-idp/conf/attributes/default-rules.xml /opt/shibboleth-idp/conf/attributes/default-rules_default.xml
wget https://docs.amres.ac.rs/download/shibboleth/default-rules.xml -O /opt/shibboleth-idp/conf/attributes/default-rules.xml
Konfiguracija Shibboleth IdP Logova¶
Konfiguracija logova vezanih za LDAP greške u autentifikaciji:
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/logback.xml -O /opt/shibboleth-idp/conf/logback.xml
Podešavanje interfejsa¶
Preuzeti korisnički interfejs na lokaciju /opt/shibboleth-idp/:
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/css.tar.gz -O /opt/shibboleth-idp/edit-webapp/css.tar.gz ; rm -Ir /opt/shibboleth-idp/edit-webapp/css
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/images.tar.gz -O /opt/shibboleth-idp/edit-webapp/images.tar.gz ; rm -Ir /opt/shibboleth-idp/edit-webapp/images
tar -xzf /opt/shibboleth-idp/edit-webapp/css.tar.gz && rm -f /opt/shibboleth-idp/edit-webapp/css.tar.gz
tar -xzf /opt/shibboleth-idp/edit-webapp/images.tar.gz && rm -f /opt/shibboleth-idp/edit-webapp/images.tar.gz
Uneti logo vaše institucije u direktorijum: /opt/shibboleth-idp/edit-webapp/images
- Imate mogućnost da unesete 2 logo fajla, jedan na srpskom i engleskom i shodno tome treba dati naziv formata npr. institucija_logo_sr.jpg i institucija_logo_en.jpg
- Dimenzije: širina do 200px.
- Podatak o logou institucije treba uneti u kasnijim koracima u fajlove messages_sr.properties i messages_en.properties
Prevod interfejsa i sistemskih poruka se preuzima u direktorijum /opt/shibboleth-idp/messages
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/messages_sr.properties -O /opt/shibboleth-idp/messages/messages_sr.properties
Potrebno je izmeniti preuzet fajl messages_sr.properties i dodati adekvatne podatke vezane za naziv vaše institucije,naziv logo fotografije i imejl adresu administratora koji će održavati ovaj IdP
Izmeniti parametre:
- idp.title=Institucija Web SSO
- idp.logo=/images/institucija_logo_sr.jpg
- idp.footer=Kontaktirajte nas na imejl adresu xxxxxxx
- root.title=Institucija Web SSO
- idp.userprefs.title=Institucija Web SSO
- runtime-error.message=.... Molimo Vas da prijavite ovaj problem službi za podršku na imejl xxxxx.
- invalid-event.message=Molimo Vas da prijavite ovaj problem službi za podršku na imejl xxxxx.
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/messages_en.properties -O /opt/shibboleth-idp/messages/messages_en.properties
Potrebno je izmeniti preuzet fajl messages_en.properties i dodati adekvatne podatke vezane za naziv logo fotografije i imejl adresu administratora koji će održavati ovaj IdP
Izmeniti parametre:
- idp.logo=/images/institucija_logo.jpg
- idp.footer=Contact us by email xxxxxxxx
Potrebno je izmeniti fajl /opt/shibboleth-idp/messages/messages.properties
Uneti sledeću liniju:
Uneti sledeću liniju uz navođenje podatka vezanog za naziv logo fotografije:
Sledi prikaz pozicije i okvirnih dimenzija logo fotografije, kao primer je prikazan logo institucije AMRES. Ova slika je informativnog karaktera za sada, tek kada se izvrši celokupna konfiguracija ova stranica vašeg IdP-a će biti dostupna za pregled.

Ilustracija logo fotografije za IdP
Preimenovanje postojećih i preuzimanje novih fajlova logout-propagate.vm, logout-complete.vm, error.vm, login.vm i logout.vm
mv /opt/shibboleth-idp/views/logout-propagate.vm /opt/shibboleth-idp/views/logout-propagate_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/logout-propagate.vm -O /opt/shibboleth-idp/views/logout-propagate.vm
mv /opt/shibboleth-idp/views/logout-complete.vm /opt/shibboleth-idp/views/logout-complete_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/logout-complete.vm -O /opt/shibboleth-idp/views/logout-complete.vm
mv /opt/shibboleth-idp/views/error.vm /opt/shibboleth-idp/views/error_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/error.vm -O /opt/shibboleth-idp/views/error.vm
mv /opt/shibboleth-idp/views/login.vm /opt/shibboleth-idp/views/login_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/login.vm -O /opt/shibboleth-idp/views/login.vm
mv /opt/shibboleth-idp/views/logout.vm /opt/shibboleth-idp/views/logout_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/logout.vm -O /opt/shibboleth-idp/views/logout.vm
mv /opt/shibboleth-idp/views/admin/hello.vm /opt/shibboleth-idp/views/admin/hello_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/hello.vm -O /opt/shibboleth-idp/views/admin/hello.vm
mv /opt/shibboleth-idp/views/client-storage/client-storage-read.vm /opt/shibboleth-idp/views/client-storage/client-storage-read_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/client-storage-read.vm -O /opt/shibboleth-idp/views/client-storage/client-storage-read.vm
mv /opt/shibboleth-idp/views/client-storage/client-storage-write.vm /opt/shibboleth-idp/views/client-storage/client-storage-write_default.vm ; wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/client-storage-write.vm -O /opt/shibboleth-idp/views/client-storage/client-storage-write.vm
Restartovati Jetty servis:
Izveštaj pokretanja skripte
INFO - net.shibboleth.idp.installer.impl.IdPBuildArguments@57fa26b7
INFO - Rebuilding /opt/shibboleth-idp/bin/./../war/idp.war, Version 5.1.2
INFO - Initial populate from ./../dist/webapp to ./../webpapp.tmp
INFO - Overlay from ./../dist/plugin-webapp to ./../webpapp.tmp
INFO - Overlay from ./../edit-webapp to ./../webpapp.tmp
INFO - Creating war file ./../war/idp.war
Restartovati Jetty servis:
Izmeniti fajl idp-metadata.xml¶
Pre bilo koje izmene ovog fajla najsigurnije je napraviti njegovu kopiju
Ovaj fajl je veoma značajan i unikatan. Iz tog razloga treba vrlo pažljivo izvršiti sve potrebne izmene i u slučaju potrebe zgodno je imati mogućnost povratka na početno stanje.
Obrisati kompletno sledeći komentar:
Kompletno obrisati sledeći segment:
<mdui:UIInfo>
<mdui:DisplayName>A name for the IdP at idp.institucija.ac.rs</mdui:DisplayName>
<mdui:Description>Enter a description for the IdP at idp.institucija.ac.rs</mdui:Description>
<mdui:Logo xml:lang="en" width="80" height="80">https://idp.institucija.ac.rs/path/to/logo.png</mdui:Logo>
</mdui:UIInfo>
Umesto tog segmenta, na istoj lokaciji dodati sledeći segment:
Izmeniti sledeće podatke:
- Naziv institucije: Uneti pun naziv institucije.
- Name of the Institution: Uneti pun naziv institucije na engleskom jeziku.
- IDP za zaposlene u instituciji: Svrha korišćenja IdP-a, npr. IDP za zaposlene u instituciji.
- IDP for staff in the Institution: Svrha korišćenja IdP-a na engleskom jeziku , npr. IDP for staff in the Institution.
- https://amres.ac.rs/dokumenti/amres_idp.png : Logo fotografija dostupna putem linka koji se navodi, širine i visine 50px.
Sledi prikaz pozicije i okvirnih dimenzija logo fotografije, kao primer je dat logo institucije AMRES. Ova logo fotografija bi se prikazala prilikom odabira Vaše institucije (Davaoca Identiteta) prilikom autentifikacije na željeni servis.
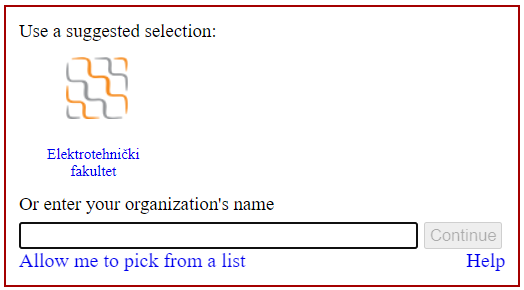
Ilustracija logo fotografije za IdP, koja se unosi putem linka
Sledeći korak:
Sledeći korak:
Dodati sledeće 2 linije tačno ispod linije <md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/Redirect/SLO"/> a pre linije <md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST-SimpleSign" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/POST-SimpleSign/SSO" />:
...
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/SOAP/ArtifactResolution" />
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/Redirect/SLO"/>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:transient</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:persistent</md:NameIDFormat>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST-SimpleSign" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/POST-SimpleSign/SSO" />
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/Redirect/SSO" />
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/POST/SSO" />
...
Ispod linije </md:IDPSSODescriptor> a iznad linije </md:EntityDescriptor> dodati sledeću sekciju:
Izmeniti sledeće podatke:
- Naziv institucije: Pun naziv Vaše institucije
- Name of the Institution: Pun naziv Vaše institucije na engleskom jeziku
- Naziv (akronim) institucije: Akronim Vaše institucije
- Naziv (akronim) institucije: Akronim Vaše institucije na engleskom
- https://institucija.ac.rs/: Link do verzije sajta institucije na srpskom jeziku
- https://institucija.ac.rs/en: Link do verzije sajta institucije na engleskom jeziku
- Ime: Ime osobe za kontakt
- Prezime: Prezime osobe za kontakt
- primer@institucija.ac.rs: Imejl adresa osobe za kontak
Fajl idp-metadata.xml nakon svih navedenih izmena:
<md:EntityDescriptor entityID="https://idp.institucija.ac.rs/idp/shibboleth" xmlns:md="urn:oasis:names:tc:SAML:2.0:metadata" xmlns:mdui="urn:oasis:names:tc:SAML:metadata:ui" xmlns:shibmd="urn:mace:shibboleth:metadata:1.0" xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<md:IDPSSODescriptor protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<md:Extensions>
<shibmd:Scope regexp="false">idp.institucija.ac.rs</shibmd:Scope>
<!-- UIInfo -->
<mdui:UIInfo>
<mdui:DisplayName xml:lang="sr">Naziv institucije</mdui:DisplayName>
<mdui:DisplayName xml:lang="en">Name of the Institution</mdui:DisplayName>
<mdui:Description xml:lang="sr">IDP za zaposlene u instituciji</mdui:Description>
<mdui:Description xml:lang="en">IDP for staff in the Institution</mdui:Description>
<mdui:Logo height="50" width="50">https://amres.ac.rs/dokumenti/amres_idp.png</mdui:Logo>
</mdui:UIInfo>
</md:Extensions>
<md:KeyDescriptor use="signing">
<ds:KeyInfo>
<ds:X509Data>
<ds:X509Certificate>
...
</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</md:KeyDescriptor>
<md:KeyDescriptor use="signing">
<ds:KeyInfo>
<ds:X509Data>
<ds:X509Certificate>
...
</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</md:KeyDescriptor>
<md:KeyDescriptor use="encryption">
<ds:KeyInfo>
<ds:X509Data>
<ds:X509Certificate>
...
</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</md:KeyDescriptor>
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:SOAP" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/SOAP/ArtifactResolution" />
<md:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/Redirect/SLO"/>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:transient</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:persistent</md:NameIDFormat>
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST-SimpleSign" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/POST-SimpleSign/SSO" />
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="https://idp.institucija.ac.rs/idp/profile/SAML2/Redirect/SSO" />
<md:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="https://idp.institucija.ac.rsidp/profile/SAML2/POST/SSO" />
</md:IDPSSODescriptor>
<md:Organization>
<md:OrganizationName xml:lang="sr">Naziv institucije</md:OrganizationName>
<md:OrganizationName xml:lang="en">Name of the Institution</md:OrganizationName>
<md:OrganizationDisplayName xml:lang="sr">Naziv (akronim) institucije</md:OrganizationDisplayName>
<md:OrganizationDisplayName xml:lang="en">Short name of the Institution</md:OrganizationDisplayName>
<md:OrganizationURL xml:lang="sr">https://institucija.ac.rs/</md:OrganizationURL>
<md:OrganizationURL xml:lang="en">https://institucija.ac.rs/en</md:OrganizationURL>
</md:Organization>
<md:ContactPerson contactType="technical">
<md:GivenName>Ime</md:GivenName>
<md:SurName>Prezime</md:SurName>
<md:EmailAddress>primer@institucija.ac.rs</md:EmailAddress>
</md:ContactPerson>
</md:EntityDescriptor>
Nakon izvršenih izmena metapodaci vašeg Davaoca Identiteta dostupni su na linku https://idp.institucija.ac.rs/idp/shibboleth
Podešavanje kolačića i ostalih podataka¶
Preuzeti skriptu updateIDPsecrets.sh na lokaciju /opt/shibboleth-idp/bin/:
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/updateIDPsecrets.sh -O /opt/shibboleth-idp/bin/updateIDPsecrets.sh
Toj skripti treba dati potrebnu dozvolu za izvršavanje:
Preuzeti CRON skriptu (/etc/cron.daily/updateIDPsecrets) koja će da je pokreće:
wget https://docs.amres.ac.rs/download/shibboleth/updateIDPsecrets -O /etc/cron.daily/updateIDPsecrets
Toj skripti treba dati potrebnu dozvolu za izvršavanje:
Proveriti da li će se skripta pokretati svakog dana (daily) :
Izveštaj provere:
Konfigurisati IdP da koristi adekvatan Attribute Filter Policy dokument¶
Kreirati direktorijum tmp/httpClientCache
mkdir -p /opt/shibboleth-idp/tmp/httpClientCache ; chown jetty /opt/shibboleth-idp/tmp/httpClientCache
Preuzeti fajl services.xml:
wget https://docs.amres.ac.rs/download/shibboleth/services.xml -O /opt/shibboleth-idp/conf/services.xml
Restartovati Jetty servis:
Proveriti status Davaoca Identiteta:
Pridruživanje iAMRES Federaciji¶
Pridruživanje iAMRES Federaciji podrazumeva razmenu metapodataka konfigurisanog Davaoca Identiteta i postojećih Davalaca Servisa. U narednim koracima potrebno je preuzeti metapodatke Davalaca Servisa iAMRES Federacije.
Preuzeti sertifikat za potpis metapodatka na lokaciju: /opt/shibboleth-idp/metadata/
wget https://docs.amres.ac.rs/download/shibboleth/md.iamres.ac.rs.crt -O /opt/shibboleth-idp/metadata/md.iamres.ac.rs.crt
Preuzeti skriptu za preuzimanje metapodataka SP entiteta iAMRES Federacije (metadata.sh) na lokaciju: /opt/shibboleth-idp/metadata/
wget https://docs.amres.ac.rs/download/shibboleth/metadata.sh -O /opt/shibboleth-idp/metadata/metadata.sh
Dati skripti odgovarajuću privilegiju za izvršavanje:
Pokrenuti skriptu:
Rezultat pokretanja skripte je kreiranje fajla iamres_federacija_metadata.xml
- Ovaj fajl predstavlja skup metapodataka Davaoca Servisa iAMRES Federacije.
Preuzeti fajl metadata-providers.xml na lokaciju /opt/shibboleth-idp/conf/:
mv /opt/shibboleth-idp/conf/metadata-providers.xml /opt/shibboleth-idp/conf/metadata-providers.xml_default
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/metadata-providers.xml -O /opt/shibboleth-idp/conf/metadata-providers.xml
Pregled fajla metadata-providers.xml sa tumačenjem njegovog sadržaja:
- U prikazanom delu fajla navode se Davaoci Servisa iAMRES Federacije, čiji su metapodaci preuzeti skriptom (./metadata.sh) i čitaju se iz gore pomenutog fajla (iamres_federacija_metadata.xml). Ovi metapodaci su potpisani sertifikatom md.iamres.ac.rs.crt.
<MetadataProvider
id="iAMRES"
xsi:type="FilesystemMetadataProvider"
metadataFile="%{idp.home}/metadata/iamres_federacija_metadata.xml">
<MetadataFilter xsi:type="SignatureValidation" requireSignedRoot="true" certificateFile="/opt/shibboleth-idp/metadata/md.iamres.ac.rs.crt"/>
<MetadataFilter xsi:type="RequiredValidUntil" maxValidityInterval="P10D"/>
<MetadataFilter xsi:type="EntityRole">
<RetainedRole>md:SPSSODescriptor</RetainedRole>
</MetadataFilter>
<MetadataFilter xsi:type="Algorithm">
<md:EncryptionMethod Algorithm="http://www.w3.org/2001/04/xmlenc#aes128-cbc"/>
<Entity>https://testsp3.amres.ac.rs/simplesaml/module.php/saml/sp/metadata.php/default-sp</Entity>
<Entity>https://ucionica.amres.ac.rs/auth/saml2/sp/metadata.php</Entity>
<Entity>https://proxy.iamres.amres.ac.rs/simplesaml/module.php/saml/sp/metadata.php/amres.ac.rs</Entity>
</MetadataFilter>
</MetadataProvider>
- U prikazanom delu fajla navode se Davaoci Servisa eduGAIN Interfederacije, čiji se metapodaci dinamički preuzimaju sa linka (http://md.iamres.ac.rs/iamres_metadata/iamres-interfederation-sp-metadata.xml). Pored toga kreira se i njihov backingFile (eduGAIN-metadata.xml). Ovi metapodaci su potpisani sertifikatom md.iamres.ac.rs.crt.
<MetadataProvider
id="eduGAIN"
xsi:type="FileBackedHTTPMetadataProvider"
backingFile="%{idp.home}/metadata/eduGAIN-metadata.xml"
metadataURL="http://md.iamres.ac.rs/iamres_metadata/iamres-interfederation-sp-metadata.xml">
<MetadataFilter xsi:type="SignatureValidation" requireSignedRoot="true" certificateFile="/opt/shibboleth-idp/metadata/md.iamres.ac.rs.crt"/>
<MetadataFilter xsi:type="RequiredValidUntil" maxValidityInterval="P10D"/>
<MetadataFilter xsi:type="Algorithm">
<md:EncryptionMethod Algorithm="http://www.w3.org/2001/04/xmlenc#aes128-cbc"/>
<!-- <Entity>https://ucionica.amres.ac.rs/auth/saml2/sp/metadata.php</Entity>-->
</MetadataFilter>
</MetadataProvider>
- U prikazanom delu fajla navode se Davaoci Servisa čiji se metapodaci unose ručno u posebnim fajlovima, u okviru direktorijuma /opt/shibboleth-idp/metadata/sourceDirectory/:
<MetadataProvider
id="iAMRESlocalDynamic"
xsi:type="LocalDynamicMetadataProvider"
sourceDirectory="%{idp.home}/metadata/sourceDirectory">
<MetadataFilter xsi:type="Algorithm">
<md:EncryptionMethod Algorithm="http://www.w3.org/2001/04/xmlenc#aes128-cbc"/>
<Entity>https://filesender-test.amres.ac.rs/simplesamlphp/module.php/saml/sp/metadata.php/default-sp</Entity>
</MetadataFilter>
</MetadataProvider>
-
Ukoliko budete imali potrebu za ručnim dodavanjem Davaoca Servisa u okviru direktorijuma /opt/shibboleth-idp/metadata/sourceDirectory/ fajlove kreirate tako što je naziv jednog xml fajla SHA-1 heš sažetak entityID vrednosti Davaoca Servisa, na koji je dodata ekstenzija ".xml" i dobija se na sledeći način:
-
Primer generisanja naziva fajla koristeći OpenSSL iz komandne linije i entityID vrednost urn:test:foobar :
Nakon preuzetih fajlova, restartovanja jetty procesa i pokretanja skripte sadržaj direktorijuma /opt/shibboleth-idp/metadata/ je sledeći:
[root@idp metadata]# ll
-rw-rw-r-- 1 jetty jetty 25921531 Aug 4 14:22 eduGAIN-metadata.xml
-rw-r--r-- 1 root root 263457 Aug 4 13:55 iamres_federacija_metadata.xml
-rw-r--r-- 1 root root 15043 Feb 7 23:16 idp-metadata_default.xml
-rw-r--r-- 1 root root 15081 Jul 21 10:56 idp-metadata.xml
-rw-r--r-- 1 root root 1980 Feb 8 10:27 md.iamres.ac.rs.crt
-rwxr-xr-x 1 root root 192 Feb 8 10:27 metadata.sh
Nakon izvršene konfiguracije i preuzimanja metapodataka, potrebno je registrovati metapodatke vašeg Davaoca Identiteta na iAMRES Federaciju, slanjem mejla sa linkom https://institucija.ac.rs/idp/shibboleth na helpdesk@amres.ac.rs.
Crontab¶
Potrebno je da se podesi da se skripta metadata.sh pokreće na svaki pun sat (u 00) svakog dana:
Uslovi korišćenja i saglasnost za slanje podataka¶
Uvesti Consent modul (modul za davanje saglasnosti):
Rezultat komande
INFO - Including auto-located properties in bin/../conf/admin/admin.properties
INFO - Including auto-located properties in bin/../conf/ldap.properties
INFO - Including auto-located properties in bin/../conf/authn/authn.properties
INFO - Including auto-located properties in bin/../conf/c14n/subject-c14n.properties
INFO - Including auto-located properties in bin/../conf/saml-nameid.properties
INFO - Including auto-located properties in bin/../conf/services.properties
INFO - Including auto-located properties in bin/../conf/admin/admin.properties
INFO - Including auto-located properties in bin/../conf/ldap.properties
INFO - Including auto-located properties in bin/../conf/authn/authn.properties
INFO - Including auto-located properties in bin/../conf/c14n/subject-c14n.properties
INFO - Including auto-located properties in bin/../conf/saml-nameid.properties
INFO - Including auto-located properties in bin/../conf/services.properties
Enabling idp.intercept.Consent...
conf/intercept/consent-intercept-config.xml created
views/intercept/attribute-release.vm created
views/intercept/terms-of-use.vm created
[OK]
Omogućiti Consent Module preuzimanjem fajla /opt/shibboleth-idp/conf/relying-party.xml
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/relying-party.xml -O /opt/shibboleth-idp/conf/relying-party.xml
Preuzeti fajl /opt/shibboleth-idp/views/intercept/attribute-release.vm:
mv /opt/shibboleth-idp/views/intercept/attribute-release.vm /opt/shibboleth-idp/views/intercept/attribute-release_default.vm
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/attribute-release.vm -O /opt/shibboleth-idp/views/intercept/attribute-release.vm
Preuzeti fajl /opt/shibboleth-idp/views/intercept/terms-of-use.vm:
mv /opt/shibboleth-idp/views/intercept/terms-of-use.vm /opt/shibboleth-idp/views/intercept/terms-of-use_default.vm
wget https://docs.amres.ac.rs/download/shibboleth/5.1.2/terms-of-use.vm -O /opt/shibboleth-idp/views/intercept/terms-of-use.vm
Izveštaj pokretanja skripte
Treba enter negde
Restartovati Jetty servis:
Testiranje slanja atributa iz komandne linije¶
Ovu komandu je moguće koristiti nakon pridruživanje iAMRES federaciji, u cilju testiranja slanja atributa ka Test servisu.
Napomena: Umesto
Pregled korisnih logova¶
Jetty logovi:¶
Shibboleth IdP logovi:¶
Audit Log:
Consent Log:
Warn Log:
Process Log: